
OSCP: Thoughts
Estimated Reading Time: 13 minutes
Introduction
It seems to be a growing trend to write a blog post after sitting your OSCP, so, I figured I may as well throw my thoughts into the mix. Please bear in mind though — the majority of this post will be my own experiences with the OSCP preparation and exam. Hopefully this will be useful to people, but how I found it may be completely different to how others find it.
As many reading this may have guessed, my relative lack of activity for the past few months has been largely due to focussing on studying for my OSCP certification. I was convinced (to my own dismay) way back in May that I might be ready to go it (thanks 0day). Now, having received the confirmation email on the fourth of December 2020 (finally something good in this god-forsaken year, huh?), I am very glad that I did.
I’ve already had a tonne of questions about my experience and workflow, so I’ll use this as an opportunity to answer some of them, as well as to give my own thoughts about the coursework and examination processes. That said, discussion of the exam itself is strictly forbidden, so I will not be fielding any specific questions about that.
This is gonna be a lengthy post, so feel free to use the Table of Contents to dot around as you like. I’ve tried to make this as modular as possible, so there shouldn’t be a problem just skipping around 🙂
Timeline
One of the predominant topics I keep getting asked about is my own background, so here’s a quick timeline:
- Started an Ethical Hacking degree in September 2019, just over a year ago. As of yet we have only covered the foundations of computer science, with the first “Hacking module” currently underway in the first semester of second year.
- Signed up for the TryHackMe HackBack2 event in October 2019 as part of my university’s hacking society.
- Focussed on coursework until December, when the TryHackMe Advent of Cyber 2019 began. That was the hook. I did the challenges as soon as they were released, loving every minute of it; and finally placed fifth on the overall leaderboard for the event. During the course of the event I joined the TryHackMe Discord server, where I eventually met the mentors and friends who have kept on pushing me to move forward and improve.
- Worked on public TryHackMe challenges for a few months. In late February I started to build my own, and joined the Content Creators program which resulted in many of the walkthroughs I’ve since worked on. Throughout this period I built challenges in my own time, which I would fully recommend doing as there is no better way to learn.
- In May I was convinced to sign up for the OSCP examination, which started in early June. I opted for the 60 day package, allowing for 30 days working on the coursework, and 30 days in the lab. In practice this changed to 40 days coursework and 20 days in the lab; however, this was still enough time to complete 60 of the 66 available targets.
About the Course
Now that we’re all caught up, let’s talk about the course itself.
Coursework
The PWK coursework has a lot of material in it. The 2020 edition has 850 odd pages covering a vast range of topics. In addition to the instructional content there are exercises which, if all completed, written up, and correct, will give you an extra five points in the exam (more on this in a bit).
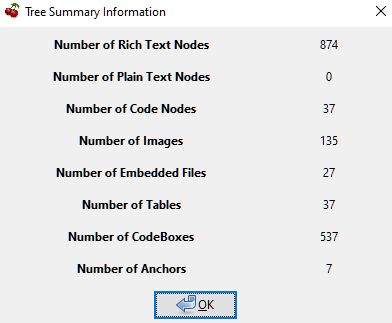
The coursework itself is really informative. My CherryTree notebook went from tiny to being the 874 Rich Text node behemouth it is today during the last six months. A lot of that is based on information learnt during PWK:
I will say that I’ve been told by more experienced mentors that some of the information isn’t the most relevant in today’s world of infosec; even so, it serves as a really good basis for many topics I hadn’t even considered before. Going straight for the OSCP as a 19 year-old, first-year student left a lot of foundations to catch up on!
As a general rule, I would say that the course work offered by Offensive Security is an absolute must read for learning — especially if you’re not coming at the exam with any other qualifications under your belt.
That said, good though the coursework is, it’s the labs which really shine.
Labs
The PWK labs really are the defining point in a prospective OSCP-candidate’s experience. The cousework gives you the basics for everything you’ll need in the labs (more on this in a bit), but it’s what you learn in the labs that really teaches you a lot.
When you first connect into the lab network you are confronted with a whole plethora of public machines to be exploited. These can be exploited in any order, so I would highly suggest performing enumeration on the entire public network before targeting any machines in particular.
The only guide you have is your lab dashboard, which allows you to submit the proof files which can be found on each target, as well as reset machines from any of the networks. That said, remember that you do have (frequently very vague) hints on the Forums, which can be used should you get stuck.
In addition to the typical “proof.txt” file, certain machines also contain a “network” proof file, which you can enter into your lab dashboard to gain access to one of the three advanced networks. Two of these can be accessed from the main subnet. The last can only be accessed by performing a double pivot through one of the other advanced networks. I’ll echo advice that I heard before attempting the labs: make sure you do the advanced networks. You won’t get nearly the full experience if you only do the boxes on the public network.
A complaint I heard frequently before starting was that the shared lab networks were overcrowded and it would be difficult to exploit machines without either running into someone who had exploited it first, or having it reset underneath you. Whilst that may well be true for some people, I can happily report that my experience was nothing of the sort. I saw another student once during my lab time; I left them alone and went to do another box, then came back to that target later on.
For the most parts the labs were really good, so I would highly recommend them.
Examination
Overview
For anyone who doesn’t already know, the OSCP examination is a grueling 24 hour experience. It starts with connecting into the proctoring session where one of the (lovely) Offensive Security proctors will guide you through setting up your exam environment. They require that all screens are shared at all times, and you must have a webcam on for your entire working time. You may not record your exam, and the proctors will be watching for any cheating.
That said, for the most part, the proctoring is not intrusive at all. It’s easy to sink into hours of no communication with them at all — although you must tell them if you intend to get up for any reason (food, toilet, sleep, breaks, etc). Due to problems with the proctoring software and the latest version of Firefox when I sat my second exam, I had to use an older browser (Slimjet) as recommended by Offensive Security. This had a nasty habit of crashing and taking my screenshares down. Fortunately the proctors were lovely about it — I just stopped working until it had sorted itself out, and they let me continue with no issues when the connection had re-established.
The exam itself consists of five targets: one easy Windows x86 buffer overflow, and four random targets which range in difficulty and are chosen at random.
The exam is out of 100 points. The buffer overflow is worth 25 points. One of the other boxes will also be worth 25. Two of the boxes are 20 pointers, and there will be one 10 pointer available. You need 70 points to pass.
During the course of the exam you can reset your five machines a total of 24 times; however, this can be reverted once during the exam, allowing for a total of 48 maximum resets. More than enough.
My Experience
I ended up sitting the examination twice, failing my first attempt in September by 10 points (and being absolutely gutted in the process); but, these things happen. I’ll talk about each of these attempts in turn.
Attempt One:
I started the exam in the early-ish morning, entirely unsure what to expect. The proctors were professional, guiding me into the exam network, then backing away to let me work through it. I started with the BoF, following the typical strategy of working on the easy 25 points whilst running AutoRecon on the other four boxes in the background. Finished the Buffer Overflow in just under half an hour with no problems, but crap! I forgot to start AutoRecon!
That was my first mistake — not the forgetting to run the tool: that’s recoverable — but I let myself panic; bad idea, especially with plenty of time left. In a frenzy I started enumeration on the other four boxes, going for the first one that looked easy: the 10 pointer. Mistake number two: I got caught up in exploiting the 10 pointer, which just did not want to be broken. I ended up spending over an hour on it without planning, wasting time.
In the end I moved on, and started flitting between the other three boxes. Mistake number three. After a few hours I found a foothold into one of the 20 pointers. 35 points. Things were looking up! Then I couldn’t find a privesc. Damn.
Switching over to the 25 pointer, I found an entry point, then rooted it soon afterwards. 60 points. Is this doable?
Unfortunately not. Sitting at 60 points, I couldn’t find a way forward.
I’d promised myself that I’d sleep when I hit 70 points. Like an idiot, I stuck to that. Mistake number 4. I ended up staying awake all night, spending hours enumerating the first 20 pointer for a privilege escalation, trying anything and everything I could think of. I kept trying the 10 pointer, eating up reverts as the software on the only open port had a publicly available exploit which crashed the software every time it ran. The software was professionally licensed with no free trial, so no hope of installing locally.
In short, I drove myself into the ground looking for a way to get that last 10 points, and failed.
Takeaways from Attempt 1:
- Don’t panic
- Sleep
- Set timers so that you never spend too much time on one thing
- Take more breaks. I was doing Ok with the breaks, but I still wasn’t taking enough
The Interim
There was a big gap between my two exams — from the start of September to the start of December. I spent a lot of this time working on projects for TryHackMe (all of which can be found on the content page), including a bunch of walkthroughs, AoC2020 Days 1 and 2, and several new boxes for my own New Year challenge series. I also spent a month working through the Virtual Hacking Labs content — a resource that I would 100% recommend to anyone looking to do OSCP. Between that and working through as much of the new TryHackMe content I’d missed whilst doing PWK, I pulled myself together for Attempt Two.
Attempt Two (Success!):
Attempt Two went so much better than attempt one. Where Attempt One was a hectic, panicked rush, Attempt Two was, for the most part, a sea of calm.
As before I started with the Buffer Overflow. This time I remembered to set AutoRecon going in the background so I had results to work with by the time the BoF fell, which it did, relatively quickly. After completing the buffer overflow, I had quick look at each of the other boxes and almost immediately found a problem with the 25 pointer, which I noted down and put aside after messing around with it for 10 minutes or so. The other targets were not hugely promising, but the 10 pointer looked to be easily exploitable. With a little modification to a publicly available script, the 10 pointer was down.
35 points, with an hour and ten minutes gone.
At this point I got stuck in a bit of a rut and started to panic again, but I pulled myself together and decided to treat each target individually. I set a two hour timer and started to work on the first 20 pointer. Close to the end of the time limit and having fallen into one hell of a rabbit hole, I switched focus and my research revealed that something that had been under my nose the entire time was actually crucial. Ten minutes later, I was in.
Unfortunately, this started following the same pattern as in Attempt One. I couldn’t root the 20 pointer. It didn’t help that it was based on a very uncommon operating system that I’d only attacked once or twice, but I persevered until the time limit ran out.
45 points.
I spent the next two hours on the other 20 pointer with no results, then went for dinner.
When I came back I started working on the 25 pointer again, and hey presto, I found another vulnerability in one of the running applications! Using a combination of this and the vulnerability I’d found at the start I managed to get user access in about half an hour. Rooting this box was incredibly easy. The time between submitting the local.txt and proof.txt files on my lab dashboard was quite literally three minutes — a welcome relief.
I had now hit 70 points — enough to pass, but I wasn’t comfortable leaving it there. I switched back to the 20 pointer I had user access to and redoubled my efforts to root it. Soon enough I found something that worked. Target number four was down. I had 80 points.
At this point I took a long break and relaxed for forty minutes or so. When I got back I started writing my report while I still had access to the exam network. By 12:30 AM it was almost finished. I had ten and a quarter hours left on the clock, with passing points and a report almost complete, so I went to bed and got a good night’s sleep.
Waking early, I went immediately back to work and finished writing up box number four. With three and a half hours of exam time left, I worked on the last 20 pointer and found the initial entry point; however, by that point, with about 20 minutes left in the exam I quite literally couldn’t be bothered exploiting it. Too much stress when I already had enough. Instead I focussed on finalising my report while I still had an exam connection to make tweaks.
The time ran out, and it was over.
I spent a few hours reading and re-reading the report, then submitted it. A day later I received a confirmation that I had passed — and here we are. OSCP down.
Reservations
The OSCP was an incredible experience, but I do have a few reservations, or comments on the process overall. This is feedback that I have already given to Offensive Security in their feedback form, but it wouldn’t feel right to not also pass it along to anyone else reading this. This is the “bad bit”, but please contrast it with the rest, all of which is good.
Exercises
Offensive Security encourage you to submit their lab report for the bonus five points, which means completing all of the exercises successfully, along with writing up 10 of the lab machines. I fully recommend not doing this, for one big reason:
The exercises are a huge time sink. They start off simple, but soon become extremely open ended. I did about 75% of them, but by the time I was 600 pages through the coursework I was writing an A4 page in answer to each question (and there were frequently two or three questions for every ten pages of coursework), and I still wasn’t convinced that my answer was what they were looking for. Lots and lots of open ended questions. Get one of them wrong, no points (or, at least, Offensive Security are very unclear about the consequences of not answering suitably, but it’s heavily implied that it’s all or nothing — get even one of them wrong and there are no bonus points). It’s just not worth the risk from a time/effort vs reward outlook.
Infrastructure
Before I start this section, I would like to make one thing clear: the majority of the Offensive Security infrastructure worked perfectly. Most of the labs worked just fine; the following notes are specific problems, but are not necessarily indicative of a greater problem.
The Offsec teaching materials are great. Their infrastructure? At times, not so much. There were multiple instances during the labs where a misconfiguration resulted in something not working: for example, in the footprinting section of the coursework, none of the Google Dorking or DNS enumeration practice examples were working. I contacted the Offensive Security support team, who acknowledged that it was a fault on their end. To the best of my knowledge, at the time of writing this still hasn’t been fixed six months down the line.
That said, once again the support offered by Offensive Security has proved to be tremendous, as I’ve recently been contacted to obtain further details of this in the efforts of obtaining a fix.
Once again, kudos to Offsec.
Learning Materials
TryHackMe
Not gonna lie — I am obviously a huge TryHackMe fan boy. It’s where I started, and it’s where I contribute. That said, I do 100% recommend it. I attribute the vast majority of my current knowledge to either things I’ve learnt at TryHackMe, or things I’ve learnt in the process of building things for TryHackMe. Virtual Hacking Labs gave me the extra boost I needed for my second exam, but TryHackMe is my base and my foundation.
Virtual Hacking Labs
https://virtualhackinglabs.com
VHL is a superb resource. They offer various “passes”, giving you temporary access to their lab environment — much like the PWK labs. Their coursework won’t give you anything you didn’t already get in the PWK coursework, but their labs (of which there are just over 40, at the time of writing) are superb practice for the OSCP exam. Pick the time limit you think you can get them all done in, and go for it.
TJNull / The Mayor List
The combined list (truncated):

TJNull’s List:
https://docs.google.com/spreadsheets/d/1dwSMIAPIam0PuRBkCiDI88pU3yzrqqHkDtBngUHNCw8/edit#gid=0
This is a resource that’s often thrown about. In all honesty, I didn’t follow it a whole lot, although a lot of my own practice (TryHackme and VHL coincided). I did all of the TryHackMe rooms (obviously), and all of the CSL boxes on the list before my first exam. I also did a fair chunk of the HackTheBox boxes on the list before attempt one. I took on all of the VHL boxes before my second attempt, which (along with the latest TryHackMe content) provided the boost I needed for Attempt 2.
Tips and Tricks
- You’ll hear this time and time again, but take breaks! My first exam attempt I ended up burnt out. My second exam attempt was much more relaxed, largely due to taking a break at minimum every two hours — often much more frequently. Trust me, you’ll thank me for the time to get your thoughts in order.
- Do the BoF first. Definitely do not ignore it. It’s an easy 25 points which can take up 20-40 minutes of your time whilst the recon is going on in the background.
- Use a tool like Tib3rius’ AutoRecon during the BoF. Doesn’t matter what tool you use, but use some kind of automator. In all honesty, this kinda throws me a little — I often end up going back and doing manual enumeration — but at the very least it gives you some results you can immediately work with.
- Remember you only need the BoF, the 25 pointer, and a 20 pointer to pass. Don’t get hung up over not doing them all — do what you need to do, catch your breath, then do whatever else you can.
- Try to get the report written before your time in the exam network ends. The writing is a lot easier if you can go back and fix screenshots. You should always have screenshots for everything, but that doesn’t mean they’re perfect, or show everything you want them to. This also means that if you’ve forgotten something, you’re able to go back and get it.
- Never sit doing nothing. Even on a break leave scans running in the background. If you have nothing else to do, try a bruteforce in the background. Try a directory or parameter fuzz. You have tools available to you — use them. They can run in the background whilst you manually look at things in the foreground.
- Don’t set unrealistic expectations. I spent most of the night in my first attempt just sitting staring at the screen with no motivation to do anything, but unwilling to go to sleep without those 70 points. Not wise. It would have been much smarter to sleep for a few hours, then wake up with a level head.
- Reset all your targets the moment you get into the exam console. They’re apparently already reset before you start, but it’s not worth the risk.
Conclusion
This has been a looooong post, so congratulations if you’ve read through it completely! As a single line conclusion: OSCP is absolutely an absolutely awesome experience, which I fully recommend going for.
It’s a struggle (“Try Harder” is the Offsec motto for a reason!), but a very satisfying one. It feels great to have this out of the way, and to be able to move on to further learning!
12 thoughts on “OSCP: Thoughts”
Hello!
Really awesome writeup!! Thank you so much for taking the time to write it! As someone who is learning, i am curious if it is possible to explain a scenario SIMILAR but NOT the same( to avoid violating rules) as the method you used for initial access on the 25 point machine? (So i can understand the main concept better) Im imagining you noticed some kind of matching exploit for a web based application on a web server, and then saw a service vulnerability or something like that in a nmap scan, but i dont know an example of how you would combine two exploits or vulnerabilities to get initial access. Is there some way you could explain a similar situation (but not the same) as a very short teaching explanation ? I want to imagine or visualize a way of doing this. At my current level i do not. (Currently did 12 easy htb boxes, and tiberius privesc courses with some PEH by cybermentor so i think i can understand concepts well enough 🙂 )
So, it would be different for each box. There are some vulnerabilities that go together really nicely. LFI and an arbitrary file upload, for example, go together really well. As a really easy example of that in particular, you might have an unsecured FTP server allowing you write access to the target, then a webapp with the LFI vulnerability which you can use to activate a shell from /srv/ftp. It’s all about taking little pieces that by themselves give something (but not everything), then stepping back and trying to fit them together to make a bigger picture. I’d suggest just performing enumeration on everything you can see, individually. Then, when you can’t find anything else, sit back and just look at what you have — can any of the little pieces be slotted together? In the end seeing that is down to practice/experience as much as anything else, so definitely keep on with THM/HTB, etc for exposure to lots of different concepts.
Thank you man. Really appreciate you taking the time to respond, (and so quickly at that!). I think this is solid advice about how to approach a problem. Thank you for your words of wisdom!
You are most welcome 🙂
Just finished your advent of cyber room 🙂 (day 2, im behind)
Great writeup man, it was inspiring, especially the Attempt 1 (no one really talks about failures, but you did, so kudos to you.)
I have a question. Are there any rabbit holes in the boxes, for example an ftp service with anonymous login, but it’s empty & you can’t upload a file as well, or a web application running, but nothing to exploit etc. etc.
If the answer to the above question is yes, then how long did you take to figure out that it was a rabbit hole, was it easy (shouting right at your face that I am a rabbit hole), or was did you spend some/a lot of time to finally realize that it’s a rabbit hole?
I can’t say much about the exam, for obvious reasons.
That said, I will say that Offensive Security are absolutely incredible at making rabbit holes — and very realistic ones at that. They don’t usually do anything blatant, but every box will have a lot going on, with very few vulnerabilities. The PWK coursework teaches you all you need to know technique wise; the exam is a test of methodology. I designed my Year of the Jellyfish to follow a similar style: lots of stuff going on, lots of moving parts, lots of distractions, but nothing blatantly unrealistic.
The trick to OSCP is time keeping. If Offsec don’t want you to know that something isn’t vulnerable (i.e. is a rabbit hole), then you probably won’t be able to figure that out within the 24 hour time limit — not without rooting the box first. Set timers for between 45 minutes and a couple of hours. If the time runs out and you don’t have any results, throw away everything you’ve tried and start again from scratch — chances are you missed something and fell into a rabbit hole without realising it.
Can you tell us a bit about your setup? PC’s, VM’s etc 🙂 thanks
Depends on when you’re meaning.
For OSCP I just used a Kali VM pre-configured for my own preferences. That would have had 8Gb RAM allocated, with 2 VCPUs (2 cores each). 60Gb hard drive, iirc. These days I would match that with either Commando or a regular Windows Server sharing a host-only network with the Kali VM, although that isn’t necessary for OSCP.
Hardware wise, I use a tri-monitor setup: VM on the first monitor, Google/Proctors on the second monitor, notes on the third monitor.
Currently waiting for GPU prices to fall before building a new PC. Suffice to say my current PC is powerful enough to run seven or eight VMs, but relatively old tech.
thanks for replying 🙂
Great blog experience, I was looking on OSCP blogs and this one contains amazing advices!
ty so much